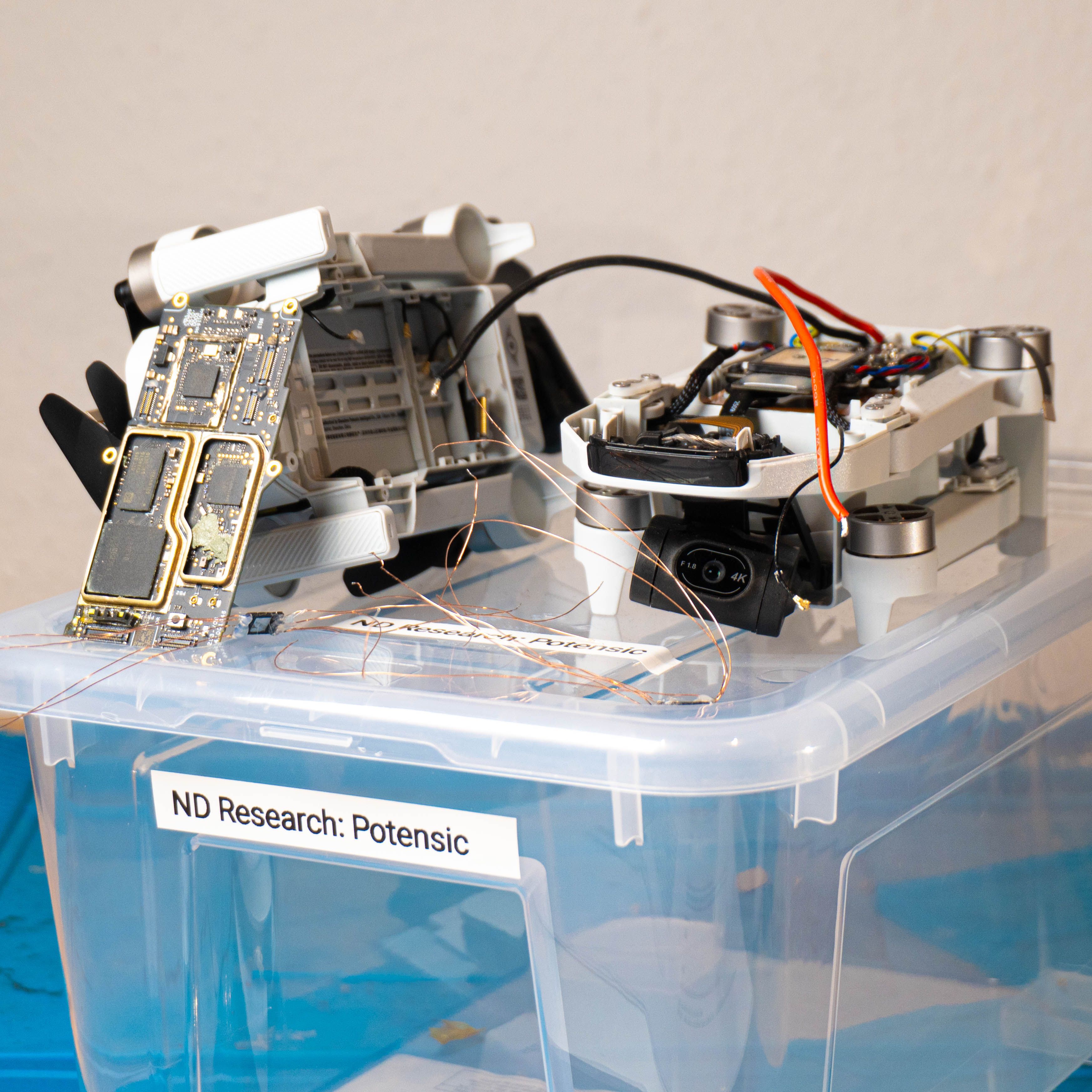
Drone Hacking Part 1: Dumping Firmware and Bruteforcing ECC
Desoldering a drone’s flash chip and reconstructing the firmware from broken data.
Our team consists of specialized security researchers who routinely uncover critical vulnerabilities in commercial software. We regularly demonstrate our expertise at events like Pwn2Own and share our knowledge as trainers at international conferences. Leverage this expertise to put your product's security to the test.
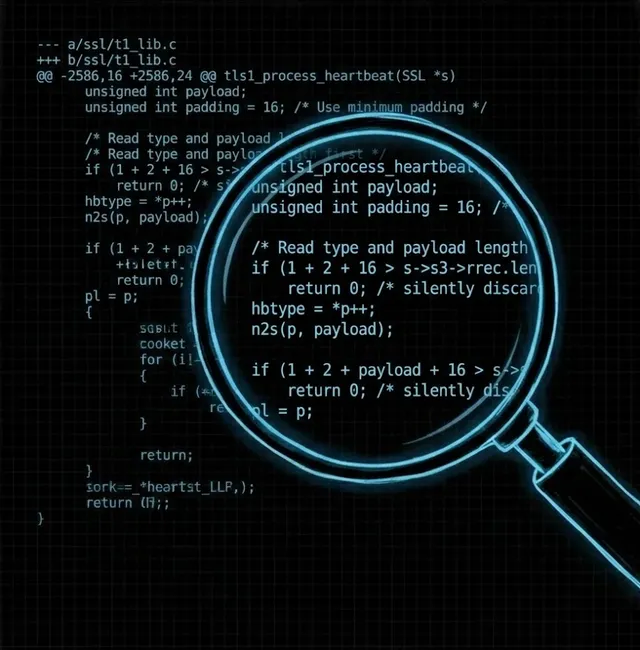
Automated tools often miss complex logic flaws and hidden vulnerabilities. That is why our experts rely on thorough manual source code analysis in all major languages (Rust, Python, C/C++, Java, C#/.NET, TypeScript, etc.). This allows us to identify even the most subtle security gaps so they can be fixed before the release.
Our security experts analyzes your Active Directory and internal network in detail. We uncover attack paths that could allow attackers to gain extensive Domain Admin privileges. Following the analysis, you will receive actionable recommendations to improve your ransomware readiness and sustainably minimize security risks.
IoT devices and embedded systems require specialized security expertise. We conduct in-depth hardware and firmware analyses to uncover vulnerabilities in communication protocols, the boot process, and physical components.
Web applications often form the largest attack surface for your business. We identify vulnerabilities in web applications and APIs by combining in-depth manual testing with modern automated tools.

Through Red Teaming, Social Engineering, or Purple Team exercises, we simulate the behavior of real attackers to test your defenses under real-world conditions. These measures provide you with a holistic view of your security posture and specifically sharpen your detection and response capabilities.

Mobile apps process sensitive data and often serve as a direct gateway to your backend systems. Therefore, we rigorously test your Android and iOS applications for security vulnerabilities. In doing so, we examine everything from local data storage to encrypted network communication.






















Our blog features posts from the world of cybersecurity, reverse engineering, research projects, solana and other blockchains, cryptography, and much more. If you're a developer, a security professional, or just an interested person, we are sure you will find something exciting to read! Here are some of our favorite posts to get you started!
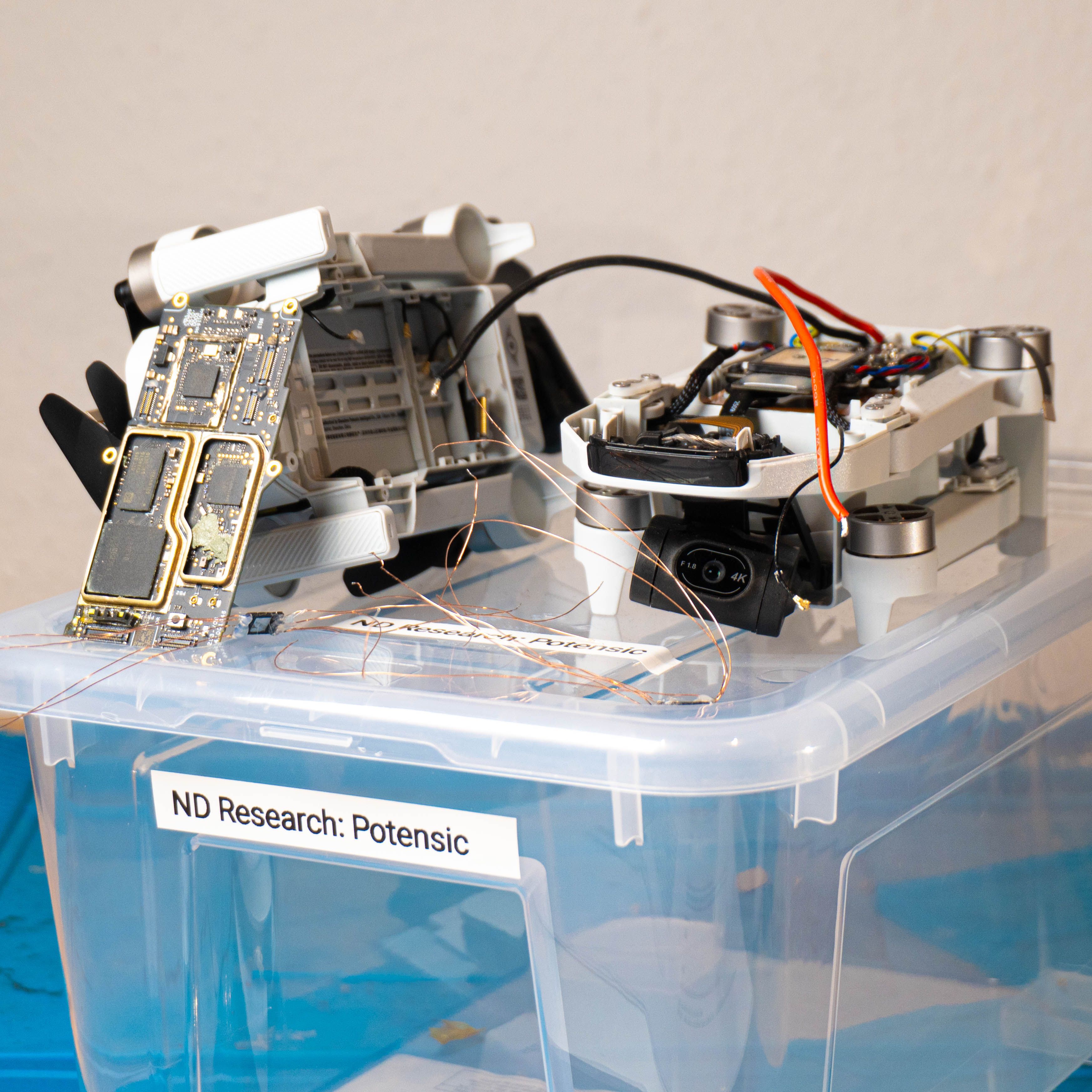
Desoldering a drone’s flash chip and reconstructing the firmware from broken data.

This blogpost starts a series about various exploits at Pwn2Own 2024 Ireland (Cork). This and the upcoming posts will detail our research methodology and journey in exploiting different devices. We start with some EXIF basics and end up with shellcode execution after reconfiguring the MMU of the RTOS.
In a recent engagement, we found an HTML to PDF converter API endpoint that allowed us to list local directories and files on a remote server. One of the PDF files we created, revealed that the converter was using a .NET renderer framework based on Chromium 62. With this, we were able to gain remote code execution by porting a Chromium 62 exploit to the particular version of the renderer.

Breaking up-to-date Windows 11 BitLocker encryption — on-device but software-only
Book your free pentest scoping call!