CVE-2026-41220 ‒ Out of bounds write in Acronis Device Lock Kernel Driver
Description
The DeviceLockDllDrv0.sys kernel driver shipped with Acronis Device Lock allows an unprivileged user to write to an arbitrary kernel address potentially leading to LPE.
Vulnerability
We found a vulnerability within the DeviceLockDllDrv0.sys shipped with Acronis DeviceLock in version (9.0.up5). The bug allows an unprivileged user to write to an arbitrary kernel address.
You can see the access rights in the following screenshot:
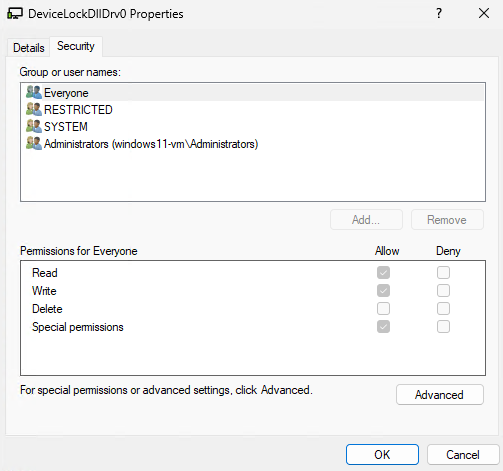
Note, that the Everyone group can read and write to the device and it is therefore accessible by users with low privileges.
The decompiled logic looked as follows:
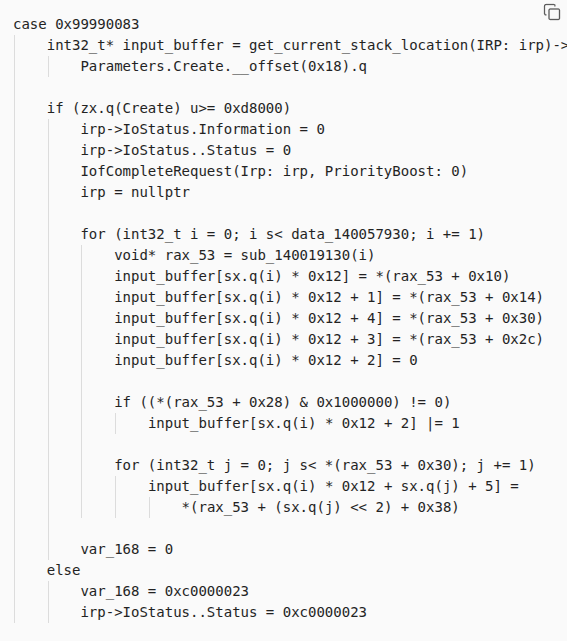
It is important to note: We are writing data into the input buffer and the IOCTL is 0x99990083. This IOCTL uses METHOD_NEITHER for the input buffer and therefore the kernel does not provide any help with managing the input buffer. Instead, it expects the driver to verify that the given input buffer actually resides in user mode and is valid. However, this does not happen here and, hence, a user can just provide a kernel address as the input buffer.
If we provide a kernel address for the input buffer, the driver will start writing to that address. If the address is invalid, this crashes the system:
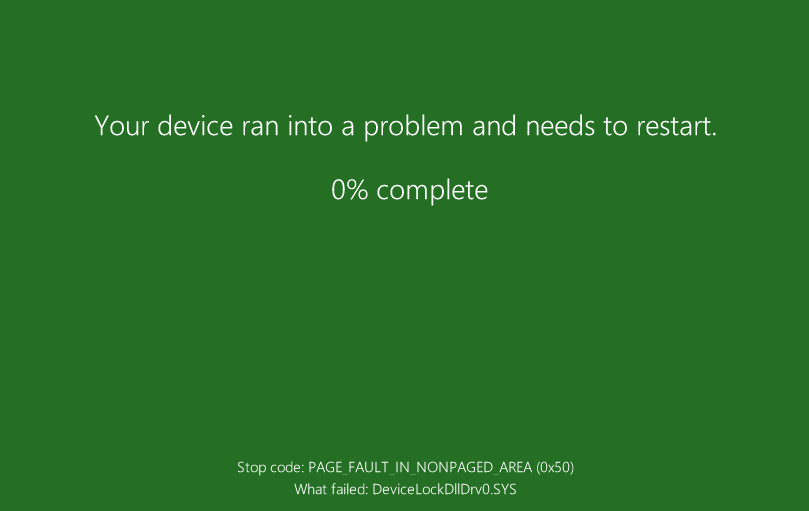
Since this vulnerability allows us to write out of bounds in the kernel, we can potentially corrupt kernel structures in-memory and escalate our privileges.
Mitigations
Update to the latest release (fixed in version 9.0.93212).
Timeline
| Date | Action |
|---|---|
| 17.01.2026 | Vulnerability found by Neodyme |
| 22.01.2026 | Vulnerability reported to vendor |
| 24.01.2026 | Report acknowledged by the vendor |
| 29.04.2026 | Public advisory by vendor |
| 06.05.2026 | Publication of this advisory |